LLMs in the Kill Chain: How AI is Democratizing Cybercrime

LLMs in the Kill Chain: How AI is Democratizing Cybercrime
The lowering of entry barriers to many technical professions has brought to light an inevitable counterpart: the adoption of Artificial Intelligence to orchestrate and automate cyberattacks.
What is the news
Between January and February 2026, a Russian-speaking attacker compromised over 600 FortiGate devices across 55 different countries.
This is reported by an investigation conducted by Amazon Threat Intelligence, which, during the described period, observed a series of attacks against devices protected by Fortinet's firewall network. The same report highlights that no evidence of bugs or vulnerabilities within Fortinet technologies was detected; rather, the acquisition of network maps and access credentials occurred by exploiting publicly exposed ports, single-factor authentication, and weak passwords.
The attack was blocked in the "pre-ransomware operations" phase thanks to an oversight by the malicious actor: the server from which they directed the attacks had been left open and publicly accessible. In this way, researchers found a real goldmine, easily extracting the indicators of compromise (IoC). This allowed for timely notification of the interested parties, who were able to mitigate the threat.
TLDR;
What made this case peculiar was not the extent of the damage (which, as we read, was limited to the "mere" access to the databases and networks of the targeted devices) nor the sophistication of the operations; quite the contrary.
The attacker was visibly someone with limited technical skills in this field. This was reported by the investigations themselves, which not only revealed the naivety of leaving an open and fully accessible trace of the server from which the attacker conducted operations, but also brought to light a series of chat logs with artificial intelligence. In these conversations, specific support was requested to carry out operations that, normally, would represent common knowledge for an even slightly more experienced hacker.
The Team
Research published on Cyber and Ramen has made known the tools used by the attacker to coordinate the offensives.
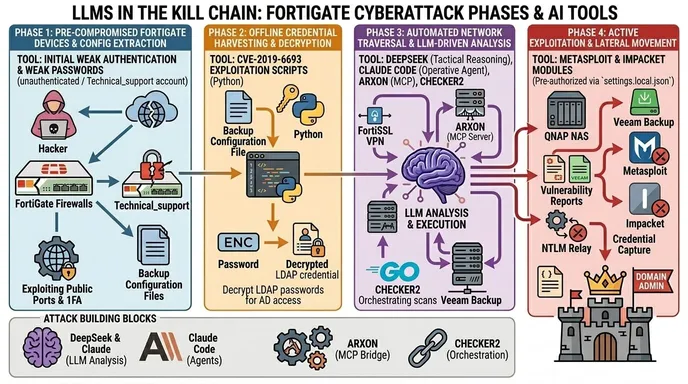
In particular, the threat actor seems to have relied on DeepSeek and Claude to perform both coordination and attack operations, asking specific questions about obtaining configurations and detecting vulnerable devices. In detail:
- DeepSeek: Used as a language model for tactical reasoning. It receives reconnaissance data (processed by ARXON) to elaborate and generate detailed step-by-step attack plans.
- Claude (Claude Code): Employed as an operative agent and material executor. Besides generating vulnerability assessments during intrusions, it was pre-authorized (via a
settings.local.jsonfile) to autonomously execute offensive tools without requiring human approval for every single command. - CHECKER2: A Docker-based orchestrator written in Go. Its main role is to automate and manage in parallel the scanning of VPNs and the processing of targets on a global scale (thousands of devices simultaneously).
- ARXON: A custom MCP (Model Context Protocol) server written in Python, acting as the main "bridge" between the attack and the artificial intelligence. It plays a dual role:
- Analysis: It receives reconnaissance data collected from the various targets, queries the AI to generate attack plans, and maintains a knowledge database that is enriched with each intrusion.
- Toolkit: It contains scripts to directly modify the victims' infrastructure, such as the massive creation of fictitious VPN accounts via SSH and the automatic validation of Domain Admin credentials.
The Attack Pipeline
The research conducted by Cyber and Ramen also made it possible to reconstruct the entire attack pipeline, demonstrating that the attacker made absolutely no attempt to cover their tracks:
- Config Extraction: The attack kicked off from already compromised FortiGate devices, accessed via a read-only administrative account (often named
Technical_support). Despite limited permissions, the account allowed the extraction of the entire backup configuration file, exposing the complete network topology (headquarters, branch offices, guest/management networks) and SSL VPN settings, including user accounts. - Credential Harvesting: The extracted configuration contained the details for LDAP authentication (used by VPN users to access Active Directory), with passwords saved in Fortinet's encrypted format (
ENC). Using Python scripts (likely linked to the CVE-2019-6693 vulnerability), the attacker decrypted these passwords offline, obtaining valid credentials for the network. - LLM-Driven Analysis: With a network map and valid credentials, the attacker connected internally via the FortiSSL VPN. At this point, the flow became automated: reconnaissance data and the results of internal network scans were sent to the AI via an MCP (Model Context Protocol) server. The attacker asked the language models to evaluate current access, find attack vectors for targets not yet reached, identify where to look for credentials in Domain Controllers, and plot the priority path to become a Domain Admin.
- Active Exploitation: In the final phase, AI-based programming agents were deployed directly against the infrastructure. The AI generated real-time vulnerability reports on internal systems (such as QNAP NAS and Veeam Backup servers) and autonomously executed, via preconfigured permissions, attack tools like Metasploit and Impacket modules to capture additional credentials, force authentication (NTLM relay), and execute remote code (RCE).
Final Thoughts
We now have, on several fronts, full evidence of the agentic reasoning and action capabilities offered by most artificial intelligence tools, even those in common use. The potential and opportunities that these tools offer are constantly growing, but at the same time, they leave themselves open to uses of all kinds.
This case shows us another important aspect: as is continuously confirmed, the weak link in cybersecurity is always the human factor.
Inexperience, overlooking some common security practices, and sometimes – perhaps – laziness, allowed both the attacker to find vulnerable devices, and the security operators to easily find the attacker.
The democratization of security is an aspect that, perhaps, more than ever in this historical period, should be mitigated with regulatory plans and greater preparation and awareness, not only on the part of those operating in the sector but also among common users.